From Promises to Proof: Verifying Security in Practice Management Software

Security in practice management software shouldn’t be an afterthought. It’s the safety net that supports client trust, clinical integrity, and responsible data storage.
Many software providers use buzzwords like “military-grade” and “bank-level” to create a sense of trust in the security levels of their product. But the truth is that although these terms sound impressive, they mean very little without the credibility of independent verification.
Real security demands more than promises.
It requires certifications like ISO 27001–accreditations earned only through rigorous third-party audits. It hinges on granular controls, transparent policies, and critically, it must be designed for healthcare workflows, not retrofitted as a sales pitch.
This article strips away the jargon. You’ll learn how to tell if a software provider is actually certified, why external audits are non-negotiable, and what questions to ask before trusting any platform with your health practice.
Why secure software matters
HIPAA and other regulations make cybersecurity non-negotiable, but selecting secure practice management software isn’t merely about meeting professional obligations. Every client interaction rests on a foundation of trust, and when you can prove that your software protects data rigorously, clients know their sensitive information is guarded not just by policy, but by design.
Think of third-party security certification as a kind of formal qualification for software providers–it exposes blind spots and weaknesses. Just as practitioners should undertake and get certified in appropriate courses for their profession, ISO-certified companies undergo audits that ensure adherence to the top security standards and reveal any vulnerabilities before they become problems.
The result? A system that verifiably provides the security guardrails it claims to have.
How to know if your software is truly secure
Secure practice management software provides evidence for its security protocols, which separates genuine security from well-intentioned claims.
Third-party certifications
We’ll say it again: Good intent isn’t enough.
Even skilled teams can overlook vulnerabilities without the benefit of added external scrutiny. That’s why third-party certifications like ISO 27001 matter–they provide an objective assessment of a company’s security posture.
ISO 27001 requires rigorous, audited processes for data protection, risk management, and continuous improvement. It’s not a one-time checklist. In fact, it can take between 3-12 months to meet certification standards, and retaining certification requires ongoing vigilance. The ISO 27001 certification is proof positive that security is embedded in software operations.
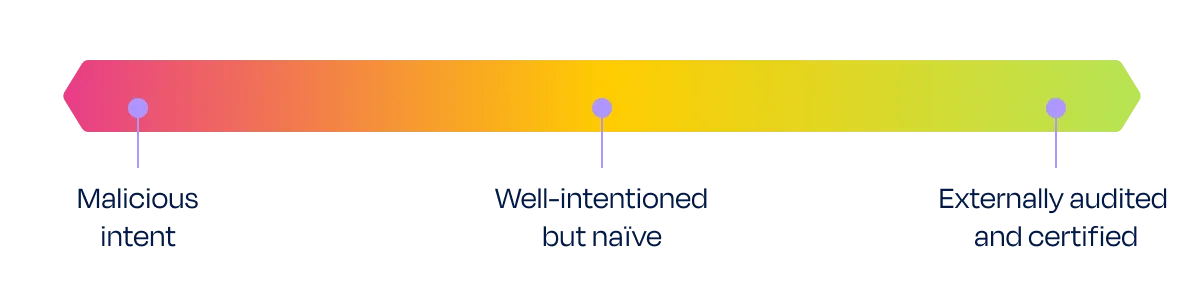
Without certification, you’re left guessing where a provider falls on the security spectrum.
Where does your software sit on the security spectrum?
External audits and penetration testing
Certifications are just the start.
When evaluating any healthcare software security, it’s important to include the following questions in your due diligence:
- Does the software provider undergo regular third-party penetration testing (essentially, mock cyber attacks that expose weaknesses in systems before hackers do)?
- Are audits routine, or just for show? Continuous evaluation ensures gaps are caught and closed.
The role of a dedicated security team
Many providers lack an Information Security Specialist, and some of these may even outsource their Data Protection Officer (DPO). These are red flags and should make you question the accountability of such software providers.
At Zanda, these are dedicated roles and these team members are embedded within our company. The security implications of every feature, update, or policy change are reviewed by our dedicated security team before implementation or rollout. Because your practice truly is our priority, Zanda believes in reliable structural safeguards, not routine rubber-stamping.
A dedicated security team shapes a company’s privacy culture, and when privacy is prioritized in every decision, complacency isn’t an option.
Red flags to watch out for
Third-party security certifications make it easy to identify software companies with strong security practices. However, surprisingly few health practice management software providers obtain them.
Why? The process is rigorous, costly, and ongoing, requiring regular reassessment to remain certified.
If a company lacks third-party certification, scrutinize their claims and think twice before exposing your practice’s (and clients’) vulnerable data to an unverified system.
Here are some specific red flags to look out for:
Red flag #1: Vague, unverifiable security claims
The company relies on flashy adjectives like “military-grade,” “bank-level,” “bulletproof,” or “vault-like” without producing concrete security certifications. They’re asking you to take their word for it, while providing no real proof of their commitment to security.
Red flag #2: Borrowed credibility
Some software companies imply adequate security by association. For example, a software company might say it uses “ISO-certified cloud servers”.
This is misleading. ISO 27001 certification must apply to the company’s own operations, not the infrastructure it leases. A vendor’s certification doesn’t automatically apply to the software built on top of it.
Tip: Ask directly, “Does the health practice management software provider itself hold the certification?”
If they deflect or imply credibility through partners, they’re aware of the gap–and hoping you won’t notice.
Red flag #3: “Compliant” vs. certified—the critical difference
Many companies claim ISO 27001 compliance without being ISO-certified, but compliance and certification imply fundamentally different levels of commitment to security.
Here’s the distinction:
- Compliant: Self-declared adherence to the International Organization for Standardization’s (ISO) standards. A company that claims it is ISO-compliant may have implemented the ISO standards relevant to its industry and may follow the guidelines prescribed by those standards. Importantly, compliance is voluntary and has not been externally checked.
- Certified: An independent auditor has verified that the company indeed adheres to ISO standards, rigorously documenting its processes and procedures. If the company meets ISO standards, it will be issued a certificate proving operational rigor.
Without third-party validation, claiming ISO “compliance” is just marketing. True security demands accountability.
Conclusion
Choosing practice management software isn’t just about choosing snappy features that simplify your workflows; it’s about choosing a guardian for your clients’ data.
Independent certifications provide you with the comfort that your software provider takes your privacy seriously.
At Zanda, we don’t ask you to take our word for it. We are ISO 27001 certified and externally audited for compliance with HIPAA and GDPR regulations. Zanda is also a member of the Australian Cyber Security Centre.
Ready to streamline your busy work with ISO 27001-certified practice management software?
Start your 14-day free trial of Zanda today–no credit card required.